
The global hospitality landscape recently witnessed a high-stakes digital standoff as Wynn Resorts navigated the aftermath of a sophisticated cybersecurity breach that targeted its internal workforce data. This incident surfaced when the notorious threat actor collective known as ShinyHunters

The modern healthcare landscape relies heavily on a complex web of interconnected service providers, yet this interdependence often introduces silent vulnerabilities that can jeopardize the privacy of thousands of patients in a single incident. Recently, Vikor Scientific, a South Carolina-based
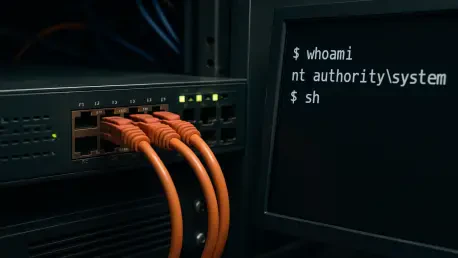
The digital infrastructure of the modern world currently finds itself in the crosshairs of a sophisticated and rapidly maturing cyber threat known as CVE-2025-55182, or more colloquially, React2Shell. What began as a theoretical risk in late 2025 has transitioned into a primary instrument for

The rapid deployment of autonomous digital entities has fundamentally altered the perimeter of the modern enterprise, turning what were once simple productivity tools into proactive participants with the power to navigate internal networks independently. This transition from traditional logic-based

The financial viability of a modern enterprise now rests on the strength of a single employee’s login credentials rather than the thickness of its digital perimeter walls. While traditional firewalls and endpoint detection remain staples of the security stack, this year marks a definitive shift
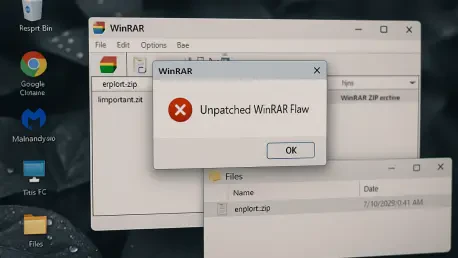
With us today is Rupert Marais, our in-house security specialist, whose expertise in endpoint security and cybersecurity strategies offers a critical perspective on today’s threats. We’re delving into a widespread vulnerability in a piece of software that many of us have used for decades: WinRAR.