Rupert Marais is a veteran in the cybersecurity field, specializing in protecting the very endpoints and networks that global healthcare platforms rely on. With years of experience managing complex digital infrastructures, he offers a unique perspective on the recent breach affecting Healthdaq, a recruitment hub serving health trusts across Northern Ireland and internationally. In this conversation, we explore the intricate layers of protecting high-stakes identity data, the challenges of third-party vendor oversight, and the technical realities of recovering from a massive data extraction by sophisticated threat actors. We discuss the immediate protocols for identity protection, the vetting process for public sector suppliers, and the ethical dilemmas of ransom demands when sensitive criminal and medical records are at risk.
Recruitment platforms often store sensitive items like passports and background checks. What specific security protocols should be prioritized to protect this level of data, and how can organizations mitigate the risk of identity theft once a breach is confirmed?
Protecting high-value assets like passports and background checks requires a “zero trust” architecture where data is encrypted both at rest and in transit. For a platform like Healthdaq, which manages nearly 500,000 files, multi-factor authentication and strict access controls are the first line of defense to prevent unauthorized extraction. Once a breach is confirmed, the recovery process must start with an immediate forensic audit to isolate the affected segments and stop the bleed. Organizations then need to notify the relevant authorities and impacted individuals, provide identity monitoring services to mitigate fraud, and rotate all administrative credentials to ensure the attackers haven’t left a backdoor.
Healthcare trusts often rely on third-party vendors to manage hiring and staff data. What are the primary challenges in monitoring these suppliers’ cybersecurity health, and what strategies should public organizations use to vet the safety of external platforms before and during a potential incident?
The primary challenge for health trusts lies in the “black box” nature of third-party security, where visibility into a supplier’s daily operations is often limited to a yearly audit. Public organizations must move beyond static checklists and implement continuous monitoring of their external platforms to catch vulnerabilities before they are exploited. Before signing a contract, it is vital to vet a partner’s incident response plan and ensure they have localized data handling protocols that align with regional privacy laws. During an active incident, transparency is the only currency that matters, requiring real-time communication between the trust and the vendor to protect the staff whose CVs and qualifications are on the line.
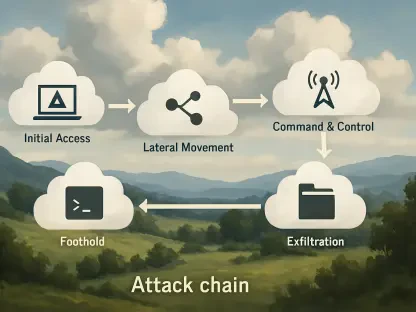
When unauthorized access to personal information occurs, what does an effective containment strategy look like for a global platform? Explain the technical hurdles of securing a system after data extraction and how organizations can restore trust with employees who are advised to remain extra vigilant.
Effective containment for a global platform involves a rapid “kill switch” mechanism that can sever connections to compromised databases without taking the entire global operation offline. The technical hurdles are immense because once data like vaccine records and government IDs have been extracted, you are essentially fighting a ghost that already has the keys to your house. Restoration of trust requires more than just a formal apology; it necessitates a radical commitment to transparency, where the company demonstrates exactly how they have fortified the environment. We must empower employees by providing them with the tools and education to remain extra vigilant, turning them from potential victims into an active part of the organization’s defense perimeter.
Hacking groups often demand ransoms after stealing vaccine records and criminal background checks. How should a company weigh the ethics of negotiating with these groups, and what specific metrics indicate that a platform has successfully closed the vulnerabilities that were originally exploited by attackers?
Dealing with a group like XP95, which claims to hold nearly half a million sensitive records, puts an organization in an impossible ethical bind where there is no “honor among thieves.” Negotiating with hackers often funds future attacks, yet the pressure to protect criminal background checks and driving licenses is a heavy burden for any executive team. To determine if a platform has truly closed its vulnerabilities, we look at metrics such as a significant reduction in the attack surface and the successful implementation of immutable logging. A successful recovery is marked by the ability to prove, through third-party penetration testing, that the specific entry point used on March 30 has been completely decommissioned and replaced with a hardened infrastructure.
What is your forecast for the cybersecurity landscape of international healthcare recruitment?
My forecast is that we will see a shift toward decentralized identity management to minimize the “honeypot” effect of centralized platforms. As long as recruitment hubs store hundreds of thousands of files in single repositories, they will remain the primary targets for sophisticated hacking groups seeking high-value personal data. We should expect more stringent regulatory requirements for third-party vendors, forcing them to adopt the same level of security as the government agencies they serve. Ultimately, the industry will have to prioritize data minimization, ensuring that sensitive documents like passports are only accessible for the shortest time possible before being moved to air-gapped storage.