
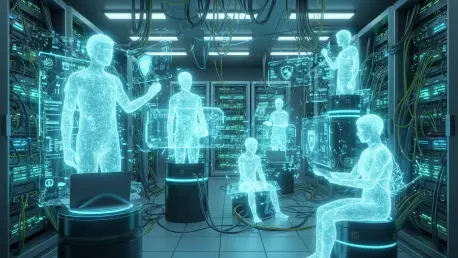
The rapid evolution of artificial intelligence from stateless, single-interaction chat interfaces into highly sophisticated agentic systems has introduced a profound architectural vulnerability rooted in the necessity of persistent memory. While these advanced systems utilize local memory

Rupert Marais is a leading security specialist at the forefront of endpoint protection and cybersecurity strategy, bringing years of expertise in managing complex network infrastructures. His deep understanding of how unauthorized parties exploit digital vulnerabilities makes him a vital voice in

A single line of malicious code in a standard Excel file was once a localized nuisance; today, when paired with an autonomous AI agent, it becomes a skeleton key to an organization’s entire data repository. The discovery of CVE-2026-26144 illustrates a jarring reality: the standard cross-site
Rupert Marais brings a wealth of experience in network management and cybersecurity strategy to the table, making him a vital voice in the conversation about evolving digital threats. As our in-house security specialist, he has watched the landscape shift from simple endpoint defense to the complex

The sudden rise of Lovable into a six billion dollar artificial intelligence powerhouse illustrates how quickly the concept of vibe coding has transformed the modern tech landscape, yet this rapid ascent recently hit a significant roadblock when a researcher revealed a massive security oversight.

Rupert Marais is our in-house security specialist with deep expertise in endpoint protection and network management. He has spent years navigating the high-stakes world of cybersecurity, focusing on how healthcare facilities can safeguard sensitive patient data against sophisticated threats. In
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62