

A multi-step conversation, seemingly harmless at first, can now systematically dismantle the safety protocols of some of the most advanced artificial intelligence systems available today, raising new questions about the fundamental security of generative AI. This discovery highlights a subtle but
A recent breakthrough from the AI safety and research company Anthropic has fundamentally altered the cybersecurity landscape, demonstrating an artificial intelligence model that can autonomously discover and detail hundreds of previously unknown, high-severity vulnerabilities in critical software.
The digital battleground has fundamentally shifted, with adversaries now favoring the quiet, methodical infiltration of networks over loud, disruptive assaults. This strategic evolution signifies a dangerous new era in cybersecurity, where the primary goal is not immediate chaos but long-term,

The European Commission has initiated a far-reaching overhaul of the European Union's regulatory framework for telecommunications and digital infrastructure by proposing two landmark pieces of legislation, the Digital Networks Act (DNA) and a revised Cybersecurity Act (CSA 2.0). Published in

Today we’re speaking with Rupert Marais, our in-house security specialist, about a recent and particularly insidious cyberattack. A state-sponsored group known as Lotus Blossom is believed to have hijacked the update mechanism of the widely-used text editor, Notepad++, to deploy a sophisticated new

A critical remote code execution vulnerability within React Native’s development environment is being actively weaponized by threat actors to deploy sophisticated malware, creating a significant and largely unaddressed risk for developers across Windows and Linux platforms. Despite active

A digital screen on a public bus flashes an arcane error message instead of its usual advertisements, a small disruption that technology experts and urban observers agree offers a surprisingly deep insight into the complex systems governing modern life. This single event, a screen displaying a
A single, easily exploitable vulnerability within one of the world's most popular file archiving tools has become the common weapon of choice for an astonishingly diverse range of global adversaries. The widespread adoption of this flaw, from elite state-sponsored espionage units to opportunistic

In a world where digital threats evolve by the minute, staying ahead requires more than just software updates; it demands deep, forward-looking expertise. We're joined today by Rupert Marais, our in-house security specialist whose work at the intersection of endpoint security and network defense
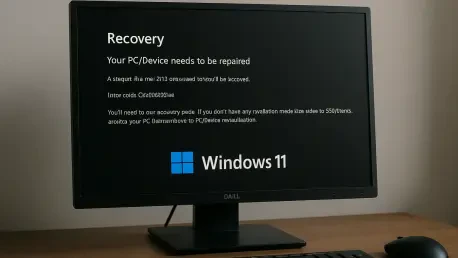
Introduction The sudden and stark appearance of a Blue Screen of Death is an unwelcome sight for any computer user, especially when it prevents the system from starting up at all. Recently, a number of Windows 11 users have encountered this exact scenario, where their machines refuse to boot
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy