

The most dangerous weapon in a modern hacker's arsenal is no longer a sophisticated piece of self-replicating code, but rather a simple ten-digit phone number buried within a perfectly mundane email. Telephone-Oriented Attack Delivery, or TOAD, has redefined the parameters of digital intrusion by
The Convergence of State-Sponsored Espionage and Cybercrime The sudden transformation of state-sponsored intelligence units into ruthless digital extortionists represents one of the most significant and alarming shifts in the modern landscape of global cybersecurity. The Lazarus Group, a notorious

The modern healthcare landscape relies heavily on a complex web of interconnected service providers, yet this interdependence often introduces silent vulnerabilities that can jeopardize the privacy of thousands of patients in a single incident. Recently, Vikor Scientific, a South Carolina-based

Rupert Marais is a veteran cybersecurity strategist and endpoint defense specialist who has spent years dissecting the evolving tactics of state-sponsored threat actors. With a deep background in network management and incident response, he currently focuses on identifying the subtle signatures

The rapid deployment of autonomous digital entities has fundamentally altered the perimeter of the modern enterprise, turning what were once simple productivity tools into proactive participants with the power to navigate internal networks independently. This transition from traditional logic-based

The rapid evolution of automated exploitation tools has created a landscape where traditional security measures often struggle to keep pace with the sheer speed and volume of modern cyber threats. Anthropic has responded to this escalating challenge by officially introducing a new AI-driven
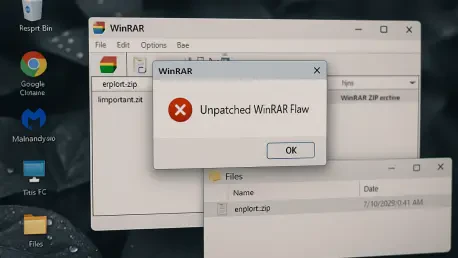
With us today is Rupert Marais, our in-house security specialist, whose expertise in endpoint security and cybersecurity strategies offers a critical perspective on today’s threats. We’re delving into a widespread vulnerability in a piece of software that many of us have used for decades: WinRAR.

The trust placed in a simple software update notification can become a gateway for sophisticated espionage, a reality recently underscored by a targeted attack that turned a trusted developer tool into a weapon. Secure software update mechanisms represent a critical line of defense in the

The rapid adoption of Artificial Intelligence presents a dual-edged sword for the modern enterprise, promising unprecedented efficiency while being fueled by data that organizations often do not fully understand. This article analyzes the critical trend of AI Data Governance, exploring the

A chilling new report reveals a significant escalation in the tactics of state-sponsored cybercrime, as a North Korean threat actor has begun integrating artificial intelligence into highly sophisticated social engineering schemes targeting the cryptocurrency sector. This group, identified as
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy