
The rapid transformation of artificial intelligence from a passive suggestion engine into an active, autonomous software engineer has fundamentally altered the digital threat landscape. Anthropic’s Claude Code and OpenAI’s GPT models have moved beyond basic autocomplete functions to become

The rapid emergence of the Coruna exploit kit, also identified by security researchers as CryptoWaters, signifies a transformative and deeply concerning era in mobile cybersecurity that challenges existing defense paradigms. Recently documented by the Google Threat Intelligence Group and further

Security leaders today must confront the reality that hardware retirement is no longer a logistical footnote but a high-stakes defensive maneuver. As data breaches continue to extract heavy financial and reputational tolls, the transition from active use to final disposal represents a critical

Every single time a user clicks a link or refreshes a private dashboard, a silent and invisible handshake occurs to ensure that no eavesdropper can intercept the flowing data. This fundamental process, known as key exchange, serves as the bedrock of digital trust by allowing two parties to

While most modern drivers worry about their smartphone location history or the onboard GPS, a much more persistent and unguarded beacon is continuously broadcasting their location from the four corners of their vehicle every single second the wheels are in motion. Every time a car travels down a

Rupert Marais has spent years on the front lines of digital defense, specializing in endpoint security and the complex architecture of large-scale network management. As an in-house security specialist, he has navigated the high-stakes world of breach response, helping organizations fortify their

The digital landscape has transformed into a high-stakes battlefield where the traditional leverage held by cybercriminals is rapidly eroding as organizations refuse to be intimidated by extortion. Recent data reveals a startling divergence in the cybercrime economy: while the total number of

The digital transformation of the African continent has created a double-edged sword where rapid economic growth now competes with the predatory expansion of global cyber-syndicates. Operation Red Card 2.0 represents a watershed moment in the fight against digital illicit activity across the
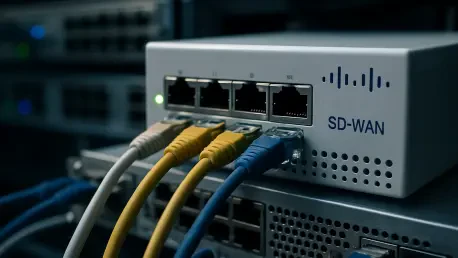
Rupert Marais is a veteran security specialist with an extensive background in securing network management planes and endpoint infrastructure. With years spent hardening large-scale enterprise environments, he provides a critical perspective on the recent warnings issued by the Five Eyes

The long-anticipated arrival of a high-stakes extraction shooter often brings a mix of excitement and apprehension regarding the technical stability and competitive fairness of the online environment. Bungie is addressing these concerns head-on as the studio prepares for the March 5, 2026 launch of
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy