

How has a seemingly secure fortress like the App Store fallen prey to advanced cyber threats? This question has gripped tech-savvy minds as a formidable new threat called SparkKitty emerges, creating ripples in the world of mobile security. Discovered by Kaspersky Lab, this sophisticated malware

In an era where cybersecurity breaches are the ever-looming shadow of technological advancement, Rupert Marais, a distinguished expert in cybersecurity and network management, sheds light on the recent trend of hackers attempting to infiltrate secure environments by masquerading as trusted
In a bustling tech firm nestled in the heart of Silicon Valley, the daily hum of business activities was abruptly silenced. The company was under siege—not from a hacker halfway across the globe, but from within its own walls. An insider attack had compromised its core systems, inflicting severe

In today's rapidly evolving digital landscape, cybersecurity threats are becoming more sophisticated and harder to detect. Joining us is Rupert Marais, an expert who specializes in endpoint and device security, to shed light on recent cybersecurity threats impacting DevOps and cloud environments,
With cyber threats becoming increasingly sophisticated, maintaining the security of network infrastructures has never been more vital. Cisco's Identity Services Engine (ISE) plays an essential role in safeguarding IT environments. However, recent reports of vulnerabilities raise significant

In an era where data is both invaluable and vulnerable, the security of backup software is pivotal. Recent revelations highlight just how susceptible backup solutions can be, particularly when they aren't updated promptly. Recent patches released by Veeam—a dominant player in the backup software

In the ever-evolving world of cybersecurity, Rupert Marais stands out as an authority. With specialized knowledge in endpoint and device security, Rupert offers invaluable insights into the current state of mobile security. His expertise helps demystify the rising threat of cyberattacks on

In a striking demonstration of the evolving complexity of cyber threats, a group known as TaxOff orchestrated an audacious cyber espionage operation, leveraging a zero-day vulnerability in Google Chrome. Identified as CVE-2025-2783, this flaw facilitated the deployment of a backdoor called Trinper,
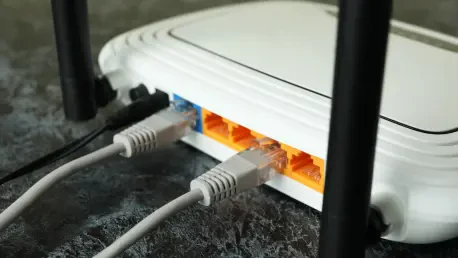
Could your wireless router be an open door for cyber threats? As personal and professional networks expand, securing digital infrastructures becomes more critical than ever. Recent reports reveal a staggering increase in vulnerabilities, with an alarming statistic indicating that over 60% of home

As digital platforms have become a staple in daily life, dark patterns pose a challenge by employing design tricks that mislead consumers into making unintended decisions. India has taken a firm stand against this by implementing strict guidelines to protect consumers from deceptive practices.
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy