

A Digital Cracks in the Foundation of a Real Estate Giant The digital keys to thousands of private lives were silently stolen from one of New York City’s most prominent real estate firms, leaving a trail of questions about industry-wide security. Rockrose Development Corp., a major player in the

With threat actors actively exploiting two critical Fortinet flaws just days after their disclosure, the race between patching and exploitation is on. We're joined by Rupert Marais, our in-house security specialist with deep expertise in endpoint and device security, to break down the technical

The familiar blue and white of a Microsoft login page has become a universal symbol of digital security, yet it is now the very camouflage used by cybercriminals to bypass an organization's most robust defenses. A sophisticated new wave of phishing attacks is turning this trusted interface into a

A digital security tool designed to be a user's vigilant sentinel against the internet's darkest corners is being retired almost as quickly as it arrived, prompting questions about the evolving landscape of online protection. Google has announced it will discontinue its dark web report feature in

An artificial intelligence agent diligently booking a vacation could, with a single malicious instruction hidden on an obscure webpage, pivot to silently draining a bank account, a chilling scenario that has rapidly moved from the realm of science fiction to a pressing reality for technology

The simple act of placing an online order unlocked a cascade of digital chaos when a meticulously planned ransomware attack crippled one of Japan's largest e-commerce and logistics firms, revealing the fragile underbelly of modern commerce. What began as a security alert quickly spiraled into a

The invisible lines between digital warfare and physical consequence are rapidly dissolving as pro-Russia hacktivist groups increasingly target the very systems that sustain modern life. This analysis dissects the alarming trend of attacks on Operational Technology (OT), exploring the tactics, key

The digital security that millions of users implicitly trust on their Apple devices was quietly and effectively compromised for an unknown number of individuals long before a public fix was ever announced. In a recent, urgent move, Apple deployed critical security updates across its ecosystem,

In an era where digital threats can cripple national infrastructure faster than any physical weapon, recent U.S. policy decisions suggest a perplexing willingness to trade long-term digital security for immediate diplomatic and economic advantages. This dynamic raises a critical question about the
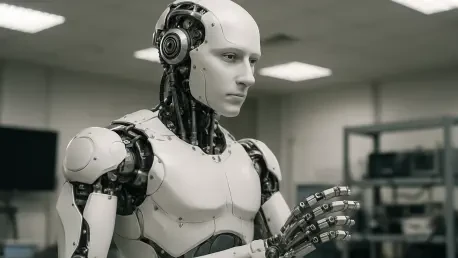
As the world stands on the cusp of an automated revolution, with advanced humanoid robots poised to integrate into factories, homes, and public spaces, a stark warning from cybersecurity analysts casts a long shadow over this promising future. Beneath the polished chrome and sophisticated
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy