
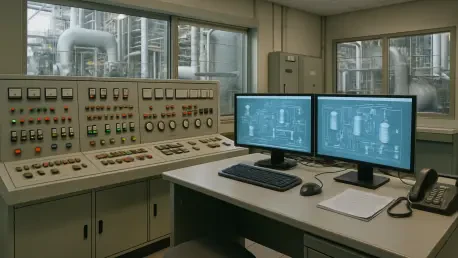
In a world increasingly reliant on interconnected industrial systems, the security of Industrial Control Systems (ICS) and Operational Technology (OT) environments has never been more critical, especially as cyber threats grow in sophistication and impact, posing significant risks to global
Setting the Stage for AI in Healthcare Imagine a world where a routine medical procedure like a colonoscopy can detect precancerous growths with unprecedented precision, potentially saving countless lives through early intervention. This is no longer a distant dream but a reality driven by

Introduction Today, we're diving into the murky waters of cybersecurity with Rupert Marais, our in-house security specialist renowned for his expertise in endpoint and device security, cybersecurity strategies, and network management. With a sophisticated phishing scam targeting UK organizations
Imagine a digital predator lurking in the shadows of the internet, striking at the heart of critical infrastructure—hospitals, energy grids, and government systems—holding them hostage for millions in ransom. This is the reality of BlackSuit ransomware, a Russia-linked cybercrime group that has
What happens when a tool as commonplace as WinRAR, relied upon by millions to zip and unzip files, becomes a secret weapon for espionage? In a chilling revelation this year, Russian hackers have been caught exploiting a critical flaw in this widely used software to spy on organizations across

Overview of the Digital Regulation Landscape Imagine a world where the open, collaborative spirit of the internet is at risk due to well-intentioned but potentially overreaching regulations that could fundamentally alter how digital platforms operate. In 2025, the digital industry stands at a
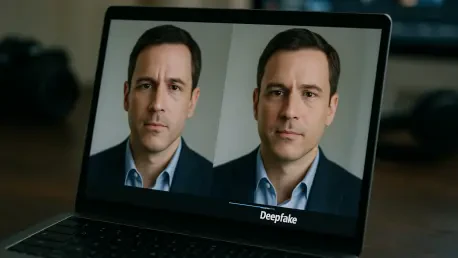
In an era where technology evolves at breakneck speed, the emergence of deepfake technology as a corporate cybersecurity threat has sent shockwaves through industries worldwide, posing unprecedented risks to financial stability. These AI-generated synthetic media, encompassing manipulated videos
Imagine a cutting-edge AI tool, hailed as the pinnacle of conversational intelligence, deployed across industries to handle sensitive data and critical decisions, only to be manipulated into providing dangerous instructions with alarming ease. This scenario is not a distant concern but a present

Introduction to Silver Fox APT and Its Dual Nature Imagine a cyber threat so versatile that it can steal state secrets one day and siphon off financial gains the next, leaving defenders scrambling to pinpoint its true intent. This is the reality posed by Silver Fox, a Chinese advanced persistent

What happens when the technology meant to safeguard digital assets becomes the very target of sophisticated attacks? In today's cloud-driven world, artificial intelligence (AI) is redefining the cybersecurity battlefield, creating a high-stakes game where innovation and vulnerability collide.
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy