

With financial scams constantly evolving, we turn to our security specialist, Rupert Marais, for his expertise in cybersecurity and fraud prevention. As criminals increasingly pivot from traditional banking fraud to the less-regulated world of gift cards, consumers are facing new and insidious
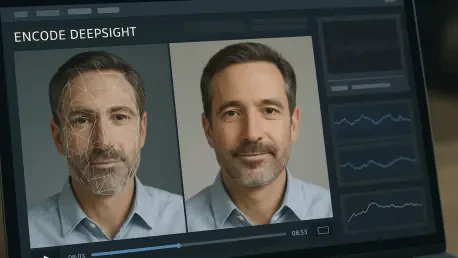
The rapid sophistication of deepfake technology has transformed what was once a social media novelty into a critical security vulnerability for businesses that depend on digital identity verification for their core operations. As synthetic media becomes more accessible and convincing, conventional
A sophisticated phishing campaign leveraging a legitimate but often overlooked Microsoft 365 feature has enabled Russian-aligned hackers to bypass conventional security measures and achieve full account takeovers against critical Western targets. This method, known as device code phishing, subverts

With us today is Rupert Marais, our in-house Security Specialist, whose expertise in endpoint security and cybersecurity strategy offers a vital perspective on digital threats. We’ll be exploring the recent University of Sydney data breach to understand the deeper issues at play. Our conversation

The Dawn of a New IT Paradigm A profound shift is underway in the information technology sector, one that promises to redefine the very nature of IT services. The recent appointment of former Palantir CIO Jim Siders to lead Shield Technology Partners, a new venture backed by over $100 million, is

In the fast-paced world of cybersecurity, staying ahead of threats is a constant battle. This month’s security updates from Microsoft are a stark reminder of that reality, with patches for 56 flaws, including one being actively exploited and two publicly known zero-days. To help us decipher the

In the murky aftermath of a digital assault on a nation's economic lifeline, the battle for the truth often proves more challenging than the fight against the malicious code itself. When Venezuela's state-owned oil company, Petróleos de Venezuela (PDVSA), experienced a significant systems failure,

Today, we're joined by Rupert Marais, our in-house security specialist, to dissect the groundbreaking announcements from Microsoft's recent Ignite conference. The tech giant is fundamentally changing how enterprises access and use AI in cybersecurity by bundling its powerful Security Copilot with

The traditional battle lines of cyberspace are rapidly dissolving as politically motivated hacktivist groups paradoxically embrace the purely commercial Ransomware-as-a-Service model, creating a new and unpredictable breed of threat actor. This emerging trend presents a fascinating contradiction:

The rapid emergence of agentic AI developer tools has fundamentally altered the landscape of software engineering, promising unprecedented efficiency gains while simultaneously introducing a new class of complex security vulnerabilities. Agentic AI developer tools represent a significant
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy