In today’s digital businesses, we rely on commercially procured or internally developed applications.
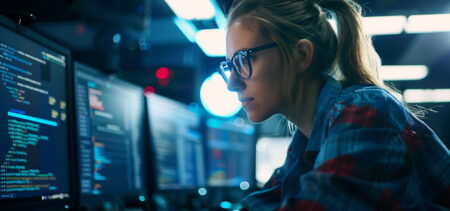
Because of the need for more speed and more routes to market a variety of things, we have an increasingly automated IT infrastructure that is fundamentally built upon a potentially weak security posture.
While application needs and capabilities and IT environments vary significantly among organizations, one thing remains true everywhere: Every application, script, automation tool, and other non-human entity relies on some form of a “secret” — or privileged credential — to access other tools, applications, and data.