
The landscape of international cyber warfare has entered a volatile new phase where state-sponsored operations are no longer satisfied with the mere theft of intellectual property or the temporary encryption of databases for ransom. Iranian-aligned threat actors have increasingly prioritized the

The rapid transformation of the digital threat landscape has resulted in a global environment where cybercriminal syndicates now function with the same logistical precision as multinational corporations, moving away from centralized structures toward a more agile and decentralized marketplace. In

The velocity of modern ransomware attacks necessitates a defensive posture that operates at machine speeds rather than relying on human intervention to mitigate threats before they traverse the network. Microsoft Defender for Endpoint has introduced a sophisticated automated response capability
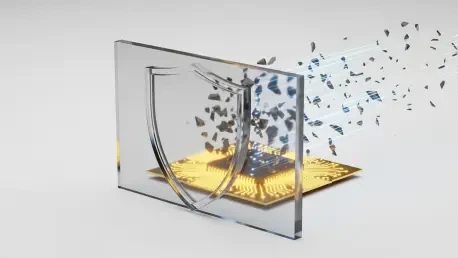
The era of the methodical, human-led cyberattack has abruptly ended, replaced by autonomous software capable of compromising an entire enterprise network before a security analyst can even finish their first cup of coffee. Historically, cybersecurity professionals relied on the concept of "dwell

The digital perimeter of modern enterprises has become increasingly porous as remote work and hybrid cloud environments continue to expand the attack surface exponentially. Despite the availability of sophisticated VPNs and zero-trust network access solutions, many organizations still rely on the

The cybersecurity landscape has undergone a radical transformation as attackers shift their focus from brute-forcing passwords to exploiting the sophisticated identity trust chains that underpin modern cloud computing environments. In a recent and highly publicized breach, Vercel became the focal
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32