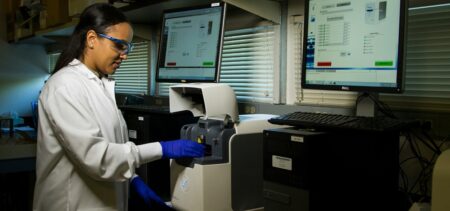
There is serious personal risk associated with a healthcare data breach, especially with multiple connected devices and health record systems generating and storing a patient’s sensitive health data.
Every person interacting with an online system needs a digital identity, and it should be authenticated in real time, so that unusual behavior can be detected at any time, whether at login or midway through a session.