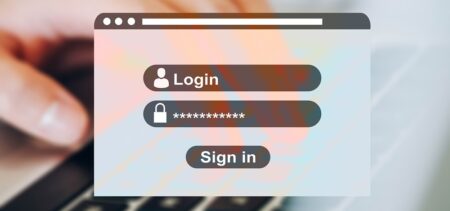
What are the most effective types of security controls and end user training approaches to dealing with phishing?
Fraudulent and malicious electronic mail continues to be a favored method for attackers to create a network breach from the inside. Like the famed Greek horse at Troy, years of work on an impenetrable outside wall can be undone from the inside with the click of a mouse.